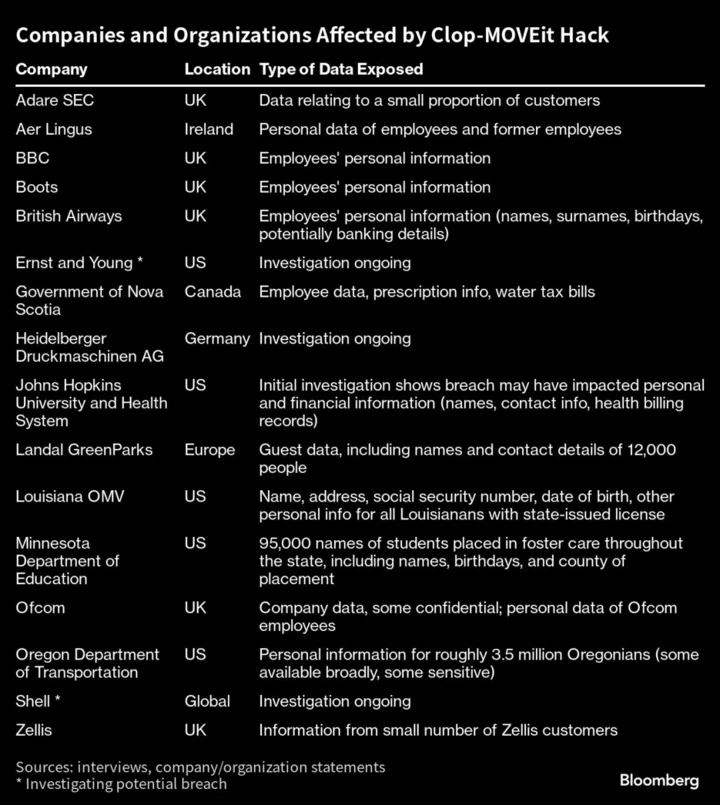
Shell Plc, IAG SA’s British Airways, the British Broadcasting Corp., the state of Minnesota’s Department of Education, multiple federal agencies — they’re among the victims of the latest data breach launched by Clop, a Russian-speaking hacking group that’s attacking targets around the world in both the public and private sectors.
The Clop gang, also known as Cl0p, is known for “driving global trends in criminal malware distribution,” according to the US Cybersecurity and Infrastructure Security Agency, or CISA. Clop has pulled off its latest breach by exploiting a weakness in MOVEit, a file-transfer product that companies and organizations use to transmit sensitive data. Once the hackers penetrated MOVEit, they could access data stored on MOVEit servers, a portal that’s enabled them to steal personal information from industry giants with tens of thousands of employees and government agencies that handle data, some of it sensitive, on millions of people. Clop is the name of a variant of ransomware, a type of malware used to encrypt a victim’s computer files in lieu of a payment. It is also the name of a financially motivated criminal gang that uses a variety of methods to extort its victims: by deploying ransomware and demanding payment; by stealing sensitive documents and threatening to post them online unless a payment is made; or both.
Clop has been honing just this sort of breach for years, researchers at Kroll LLC, a private-intelligence firm, have found.
It appears to be one of their signature attacks. A few years ago, Clop leveraged software flaws in a file-transfer product made by a company then known as Accellion to access data from Morgan Stanley, Jones Day, and Kroger among others. Accellion has since changed its name to Kiteworks.
Earlier this year, the group claimed credit for a hack on a different file transfer product called GoAnywhere, from Fortra LLC.
“This finding illustrates the sophisticated knowledge and planning that go into mass exploitation events such as the MOVEit Transfer cyberattack,” ones where intruders use a single point of vulnerability in an attempt to compromise as many victims as possible, the Kroll researchers said.
Cybercrime experts say they first came to know of the group’s malware in 2019, when it launched a phishing campaign as part of a series of ransomware attacks against Korean companies and US academic institutions. The list of targets soon expanded to include financial, insurance, manufacturing and communications companies across the world, according to Trend Micro, Inc., a cybersecurity firm.
By 2021, the group was flaunting its success. That February, its page on the dark web — known as a shaming site — included a long list of victims in places like the US, Singapore, and The Netherlands, security firm Mandiant Inc., reported.
In June of that year, Ukrainian police said they arrested multiple suspects who, they alleged, worked with Clop ransomware to extort organizations in the US and South Korea. According to law enforcement officials, the group fleeced victims out of $500 million.
"The Clop ransomware group has been a persistent and damaging threat actor,” said Michael DeBolt, chief intelligence officer at Intel 471, a cyber threat intelligence firm. “The vulnerability used by the gang was unknown prior to the start of attacks, which put organizations using the software in a mostly defenseless position. The use of such a vulnerability before it is publicly known means Clop has the resources and ability to develop or acquire such capabilities.”
Like other Russian-speaking ransomware groups, Clop has avoided targets in former Soviet countries. In fact: its malware can't even breach a computer that operates primarily in Russian, the Korean cyber firm AhnLab has found.
But it hasn’t shown much restraint elsewhere. Clop has been known for targeting the health-care sector, and in 2022, it took credit for an attack on a UK company that supplies water to more than 1.5 million people. In a statement on its dark web site at the time, the Clop group claimed it stole a trove of data and had gained access to systems that control chemical levels in the water. “If you are shocked it is good,” the group said.